STEP-BY-STEP GUIDE: SECURING AI ENDPOINTS AND INFRASTRUCTURE WITH FLOWTRIQ
>>DDoS protection doesn’t need to be theatre. It just needs to work — fast.
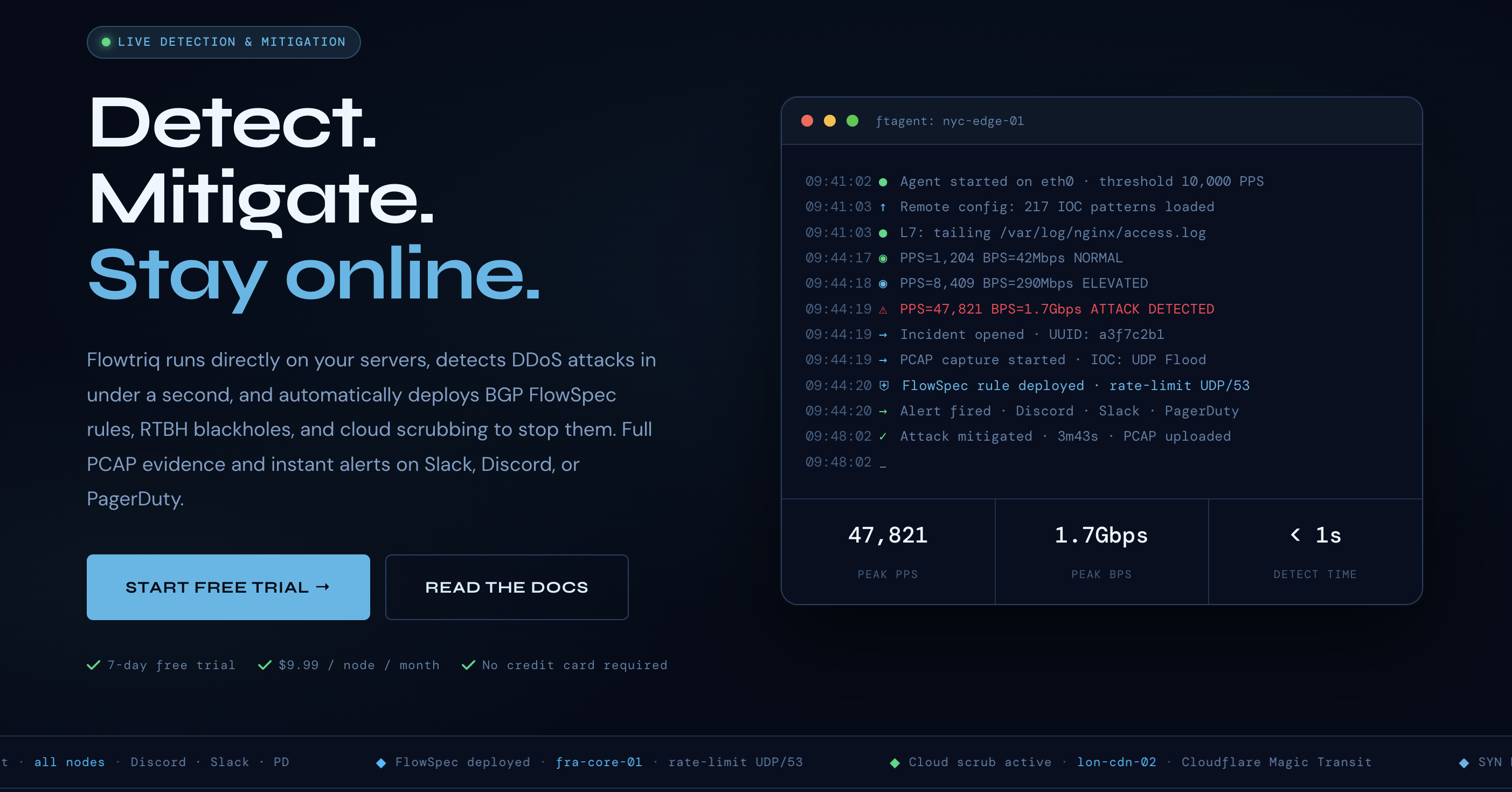
Most DDoS solutions sell drama: dashboards full of graphs, armies of rules, and invoices that scale with your traffic. Flowtriq is refreshingly boring in the best way — a tiny Linux agent that watches packets, learns what “normal” looks like, and flips auto-mitigation into play before your users notice. If you run game servers, a small hosting stack, or ML model endpoints that can’t tolerate minute-long outages, this is the practical alternative to big-cloud scrubbing bills and manual fiddling.
I spun up Flowtriq after a spike knocked a staging model offline. Within minutes the ftagent was logging packet-level anomalies and triggered an RTBH route that kept the model reachable while we investigated — priceless. Now, here’s how you do it.
>>Step 1: Setting Up Your Account
- Sign up on Flowtriq (7-day free trial; no credit card). I recommend using a dedicated account for infra alerts, not your personal email.
- Create a node in the dashboard for each server you’ll protect.
- On the node page, copy the installation snippet for ftagent. It’s a Python installer you run on any Linux server — usually under two minutes.
- Example: ssh into the server, paste the command, and let it install. The agent reads packets from the NIC and connects to the cloud automatically.
- Configure credentials for any downstream mitigations you want: BGP FlowSpec (router credentials), RTBH (BGP route targets), and cloud scrubbing (Cloudflare Magic Transit, OVH VAC, Hetzner).
- Set alerting channels: Slack, Discord, PagerDuty, or webhooks. I push to a dedicated Slack channel and a webhook that feeds our ML ops pipeline.
>>Step 2: Core Features You Need to Know
- Sub-second detection and automated mitigation
- ftagent checks PPS every second and will deploy FlowSpec/RTBH or cloud scrubbing according to your escalation policy. Meaning: mitigation before users call support.
- Dynamic baseline learning
- Let the agent run for a baseline-learning window (few hours to a day). It adapts thresholds to your actual traffic so you avoid false positives during rollouts.
- PCAP capture on every attack
- Automatic full-PCAP capture is saved for forensics. Download these to analyze bot behavior, retrain anomaly detectors, or feed into threat research.
- IOC correlation & attack classification
- Flowtriq matches traffic against 642k+ IOCs (includes Mirai variants) and classifies attack types (SYN, UDP, DNS amp, L7 floods, etc.) to choose the right mitigation chain.
- Automated incident runbooks
- Chain steps into playbooks: e.g., try FlowSpec, then RTBH, then cloud scrubbing. Keeps human ops out of the loop until necessary.
>>Step 3: Pro Tips for Artificial Intelligence Professionals
- Use PCAPs to build better NIDS and adversarial datasets — label attack traffic and incorporate into your anomaly models.
- Integrate webhooks into your ML pipeline so a detected attack can trigger a model rollback or throttle rollout of a new model version.
- During traffic surges for model retraining jobs, temporarily widen baselines or create maintenance windows so flows aren’t misclassified.
- Use attack profiles to simulate targeted Layer 7 floods against your inference endpoints before pushing new models to production.
- Keep an eye on IOC hits — novel IOC patterns could indicate poisoned training attempts or targeted data exfiltration through layer-7 abuse.
>>Common Mistakes to Avoid
- Skipping the baseline-learning period — you’ll get avoidable mitigation during normal spikes.
- Not configuring escalation credentials in advance — when an attack hits you don’t want to scramble BGP creds.
- Flooding your team with alerts — set critical channels for paging and less-urgent channels for logs.
- Assuming cloud scrubbing is automatic — you still need vendor credentials and agreements set up.
- Ignoring PCAPs — those captures are gold for root-cause and improving ML defenses.
>>How It Compares to Alternatives
Flowtriq is lightweight and agent-first, which contrasts with big scrubbing services that route your traffic through the cloud or charge per-GB. Compared to Cloudflare/Akamai/Corero, Flowtriq:
- Excels at sub-second, on-host detection via ftagent.
- Offers flat per-node pricing ($9.99/month) rather than traffic-based billing.
- Adds automatic PCAP capture and IOC correlation out of the box. If you need enterprise-grade global scrubbing at massive scale, other vendors may still win — but for hosting providers, game servers, edge operators, and AI infra with tight cost constraints, Flowtriq is an elegant, autonomous option.
>>Conclusion: Is Flowtriq Right for You?
If you run Linux servers that can’t afford long outages, want automated, fast mitigation, and like predictable pricing, give Flowtriq a spin. I run it in my lab and trust the PCAPs and automated playbooks when I push new models. The future is autonomous. We shouldn’t be babysitting mitigations — Flowtriq lets you focus on building, not firefighting. Try the 7-day free trial and see if your incident volume drops before your coffee gets cold.